Published By
Created On
9 May 2022 15:58:22 UTC
Transaction ID
Cost
Safe for Work
Free
Yes
Chinese Hackers Caught Stealing Intellectual Property from Multinational Companies
Chinese Hackers Caught Stealing Intellectual Property from Multinational Companies
An elusive and sophisticated cyberespionage campaign orchestrated by the China-backed Winnti group has managed to fly under the radar since at least 2019.
Dubbed "Operation CuckooBees" by Israeli cybersecurity company Cybereason, the massive intellectual property theft operation enabled the threat actor to exfiltrate hundreds of gigabytes of information.
Targets included technology and manufacturing companies primarily located in East Asia, Western Europe, and North America.
"The attackers targeted intellectual property developed by the victims, including sensitive documents, blueprints, diagrams, formulas, and manufacturing-related proprietary data," the researchers said.
"In addition, the attackers collected information that could be used for future cyberattacks, such as details about the target company's business units, network architecture, user accounts and credentials, employee emails, and customer data."
Winnti, also tracked by other cybersecurity vendors under the names APT41, Axiom, Barium, and Bronze Atlas, is known to be active since at least 2007.
"The group's intent is towards theft of intellectual property from organizations in developed economies, and with moderate confidence that this is on behalf of China to support decision making in a range of Chinese economic sectors," Secureworks notes in a threat profile of the actor.
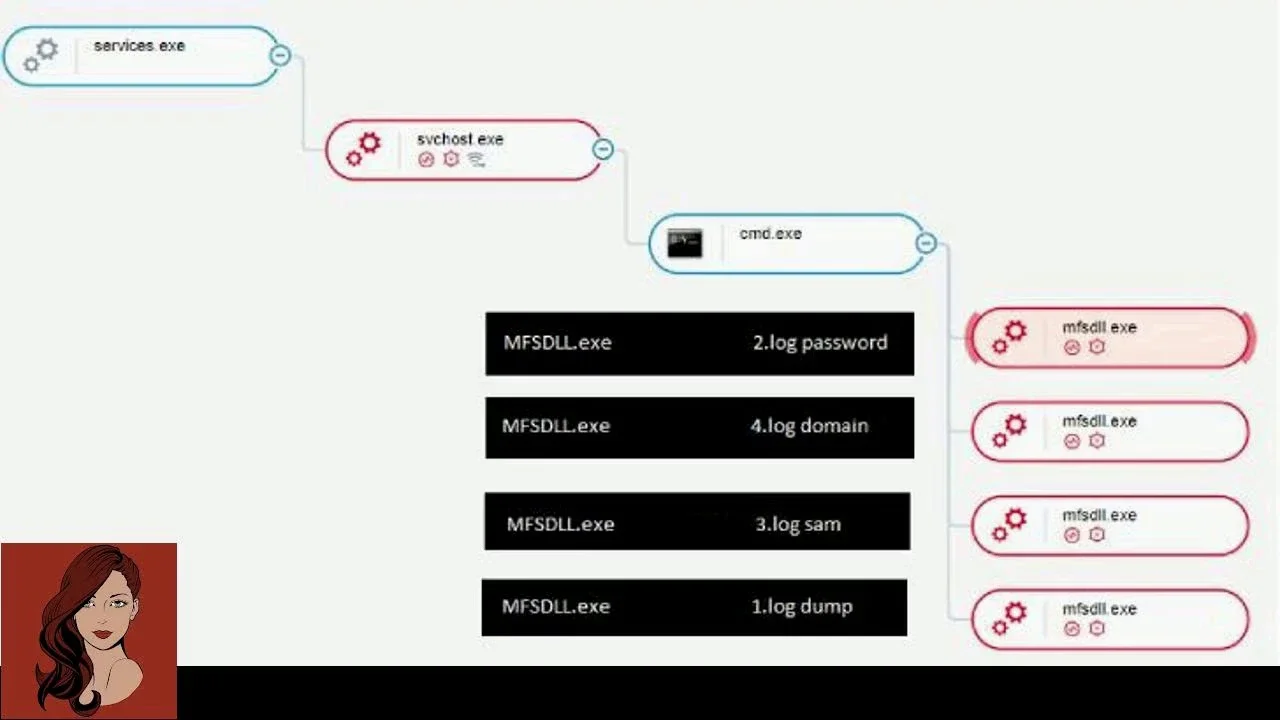
The multi-phased infection chain documented by Cybereason involves the exploitation of internet-facing servers to deploy a web shell with the goal of conducting reconnaissance, lateral movement, and data exfiltration activities.
It's both complex and intricate, following a "house of cards" approach in that each component of the killchain depends on other modules in order to function, rendering analysis exceedingly difficult.
"This demonstrates the thought and effort that was put into both the malware and operational security considerations, making it almost impossible to analyze unless all pieces of the puzzle are assembled in the correct order," the researchers explained.
The data harvesting is facilitated by means of a modular loader called Spyder, which is used to decrypt and load additional payloads.
Also used are four different payloads — STASHLOG, SPARKLOG, PRIVATELOG, and DEPLOYLOG — that are sequentially deployed to drop the WINNKIT, a kernel-level rootkit.
Crucial to the stealthiness of the campaign is the use of "rarely seen" techniques such as the abuse of Windows Common Log File System (CLFS) mechanism to stash the payloads, enabling the hacking group to conceal their payloads and evade detection by traditional security products.
Interestingly, parts of the attack sequence were previously detailed by Mandiant in September 2021, while pointing out the misuse of CLFS to hide second-stage payloads in an attempt to circumvent detection.
The cybersecurity firm attributed the malware to an unknown actor, but cautioned that it could have been deployed as part of a highly targeted activity.
"Because the file format is not widely used or documented, there are no available tools that can parse CLFS log files," Mandiant said at the time.
"This provides attackers with an opportunity to hide their data as log records in a convenient way, because these are accessible through API functions."
WINNKIT, for its part, has a compilation timestamp of May 2019 and has almost zero detection rate in VirusTotal, highlighting the evasive nature of the malware that enabled the authors to stay undiscovered for years.
The ultimate goal of the intrusions, the researchers assessed, is to siphon proprietary information, research documents, source code, and blueprints for various technologies.
"Winnti is one of the most industrious groups operating on behalf of Chinese state-aligned interests," Cybereason said.
"The threat [actor] employed an elaborate, multi-stage infection chain that was critical to enabling the group to remain undetected for so long."
Author
Content Type
Unspecified
video/mp4
Language
English
Open in LBRY
More from the publisher
LANG_en_checkyourgemsrubygemsfixesunauthorizedpackagetakeoverbugmp4
Check your gems: RubyGems fixes unauthorized package takeover bug
The RubyGems package repository has fixed a critical vulnerability that would allow anyone to unpublish ("yank") certain Ruby packages from the repository and republish their tainted or malicious versions with the same file names and version numbers.
Assigned CVE-2022-29176, the critical flaw existed on RubyGems.org, which is the Ruby-equivalent of npmjs.com, and hosts over 170,000 Ruby packages (gems) with almost 100 billion downloads served over its lifetime.
An initial audit from RubyGems reveals that the vulnerability has not been exploited within the last 18 months to alter any gems, but a deeper audit is still in progress with results yet to be announced.
Top Articles
READ MORE Hijacking a gem: yank, alter, republish This week, RubyGems announced that a critical bug could've enabled any RubyGems.org user to yank versions of a gem that they didn't have authorization for, and replace the gem's contents with newer files.
Similar to npm for NodeJS packages, RubyGems is a package manager for the Ruby programming language and provides a standardized format for distributing finished Ruby artifacts (called "gems").
The RubyGems.org registry is the community's gem hosting service allowing developers to instantly publish or install gems and use a set of specialized APIs.
Should a threat actor become aware of such a flaw, they could quietly replace the contents of legitimate Ruby packages with malware—something which has echoes of npm's popular ua-parser-js, coa, and rc libraries that were hijacked last year to distribute crypto miners and password stealers.
Although the npm hijacking incidents stemmed from maintainer account compromises rather than a vulnerability exploit, they wreaked havoc as libraries like 'ua-parser-js' have been used by over a thousand projects, including those used by Facebook, Microsoft, Amazon, Instagram, Google, Slack, Mozilla, Discord, Elastic, Intuit, Reddit, and many more well-known companies.
In Ruby's case, mass exploitation of such an exploit could cause widespread damage to the Ruby ecosystem and overall software supply chain security.
To exploit the vulnerability, RubyGems explains, the following conditions need to be met: The gem being targeted has one or more dashes in its name, e.g.
something-provider.
The word that comes before the first dash represents an attacker-controlled gem that exists on RubyGems.org.
The gem being yanked/altered was either created within the past 30 days or had not been updated in over 100 days.
"For example, the gem something-provider could have been taken over by the owner of the gem something," explains RubyGems.
"Organizations with many gems were not vulnerable as long as they owned the gem with the name before the dash, for example owning the gem orgname protected all gems with names like orgname-provider."
This vulnerability, assigned CVE-2022-29176, lurked in the "yank action" of RubyGems code and has now been fixed.
At this time, RubyGems.org maintainers do not believe the vulnerability has been exploited, according to the results of an audit that analyzed gem changes made over the last 18 months on the platform.
But the registry owners state that a deeper audit is ongoing and its results will follow in the security advisory published for this vulnerability.
"RubyGems.org sends an email to all gem owners when a gem version is published or yanked.
We have not received any support emails from gem owners indicating that their gem has been yanked without authorization," states the advisory.
User laursisask has been credited with reporting the vulnerability via HackerOne.
Transaction
Created
1 month ago
Content Type
Language
video/mp4
English
LANG_en_cryptorobberwholuredvictimsviasnapchatandstole34000jailedmp4
Crypto robber who lured victims via Snapchat and stole £34,000 jailed
Online crypto scams and ponzi schemes leveraging social media platforms are hardly anything new.
BleepingComputer has previously reported on crypto thieves abusing Instagram for running 'investment' scams that people could and have fallen for.
But, this gruesome case of a London-based crypto robber transcends the virtual realm and tells a shocking tale of real-life victims who were coerced into paying £34,000 in total to the perpetrator.
Top Articles
READ MORE
READ MORE Editor's note: some readers may find the content of this report distressing but emerging crypto robberies like the one outlined below prompted BleepingComputer to report on this case, to caution everyone.
21-year-old crypto thief gets five years in jail On Wednesday, May 11th, The Crown Court at Southwark in London sentenced 21-year-old Karim Hassan to five years in prison for pulling off multiple crypto robberies and making lethal threats to his victims, a source familiar with the specifics of the case has told BleepingComputer.
Hassan, a resident of London's Maida Vale district would use Snapchat to anonymously interact with customers looking to exchange their cryptocurrency for cash in person.
To carry out these off-the-books transactions, Hassan would ask customers to meet him in his black Audi A6.
Once in the backseat of his car, customers were asked to hand over their phones and digital wallets containing Bitcoin and crypto-assets.
Any hesitation or refusal on the person's part would rapidly turn into an ugly situation—with Hassan now threatening them with ghastly violence and even sexual assault.
Zain Hankin, one of the victims of this bootleg scheme had video-called Hassan prior to meeting up with him.
But upon refusing to give his phone to Hassan, Hankin was quickly threatened to "do something before I stick it in your neck," states the victim's statement.
After being held at knifepoint in the Audi, Hankin had little choice other than to give away his crypto worth £20,000 to the perpetrator.
This is despite the fact, Hankin had been accompanied to the meeting by a trusted friend who waited outside the car as Hankin joined Hassan alone in the backseat.
At one point during the course of the "transaction" Hankin's friend even knocked on the driver's window to ask for a cigarette—making sure everything was alright, but with a knife held next to him, Hankin couldn't give a distress signal in time.
In a similar fashion, another victim, Abbas Mamuod was forced into paying Hassan over £10,000 after being threatened with a pocketknife.
All such involuntary transactions would be made from victims' smartphones, authorized by their fingerprints.
Crypto theft was preceded by violence, rape threats In some cases, Hassan would describe himself as a "killer" who was anyway going to jail and was "going to stab you in the neck."
Sometimes, he would allegedly go to the extent of physically assaulting victims or threatening them that he'd cut off their fingers "one by one," should they refuse to cooperate, the same source familiar with the matter told BleepingComputer last week.
A summary of the case published on Court News UK this week also confirmed the veracity of these claims.
Abdullahi Goloid is one such victim who states he was taken to an underground parking lot only to be punched multiple times by Hassan and another unknown male.
The offenders then terrorized Goloid by warning the victim that he would be tied up, stripped, and raped.
After enduring this arduous episode of struggle, Goloid handed over £2,500 to Hassan.
But, Hassan's fate was sealed after this incident.
Luckily, Goloid took note of the Audi's registration plate number and reported it to the police.
A few days later, police officers spotted Hassan driving the vehicle and stopped him for a search.
Not only did the defendant's description match what had been described by Goloid, but officers obtained items such as a credit card and a jacket stolen from a previous victim.
This made it possible for the police to track down the victim named on the credit card who then positively identified Hassan on November 11th, 2021 as a perpetrator—two days after being robbed by him.
Although Hassan was often joined by others in orchestrating these crimes, he was the "prime mover" behind the scam operation that he ran via online messaging apps.
On the surface, this may look like any old robbery but the nature of goods stolen—cryptocurrencies in the vast majority of crimes, made it greatly challenging for the prosecution to proceed against the accused, our source tells us.
Establishing the link between crypto transactions—showing money changing hands between wallets, or even understanding and explaining what was going on in a legal context proved out to be difficult.
Hassan's barrister, John Oliver acknowledged the seriousness of his client's crimes and mentioned Hassan's "troubled family background" and having to "ste
Transaction
Created
1 month ago
Content Type
Language
video/mp4
English